This article will explore methods for “hiding” SSH servers so that the server is harder to discover by malicious users on public networks. We’ll focus on changing the default SSH port and implementing SSH port knocking to make it more difficult for unwanted users to discover or locate the server. This is a technique known as security through obscurity and is fun to implement but it is not wildly practiced as it does not play well with automated SSH access and adds operational complexity of implementation if you have multiple SSH servers.
To follow this tutorial, you need:
sudo privilege to perform configurations shown in this post.Changing the default SSH port is the first step to hide our SSH server. In this case, we’ll assign port 60636, but you can use any custom port number of your choice. To begin, open your terminal and connect to your server via SSH using this command:
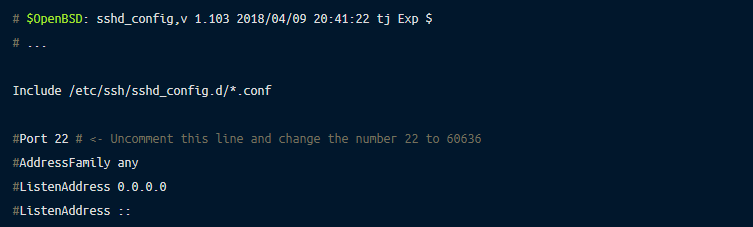
When you’re on the server, open the SSH config file with the vi command in your terminal or with any text editor of your choice:
Now update the default port 22 to 60636.
Once that’s done, restart the SSH server daemon so that the update is applied to all new incoming SSH connections.
The SSH server will now accept new connections on port 60636, and to connect, you should supply the port number as the following:
Note that if you have configured a firewall on this server, you should also update the rule to allow SSH on port 60636 and block SSH on port 22.
The port knocking technique grants a user access to an SSH server without permanently opening the port. In this technique, an SSH port is disabled by default, and the user needs to initiate the specific knock sequence to open the port. The SSH port is opened only if the user performs a successful sequence. Opening and closing the SSH port is automatically handled by knock programs such as knockd.
To implement port knocking, we’ll install knockd on the Linux server. Run the following command to install knockd:
Then, open the knockd configuration file located at /etc/knockd.conf:
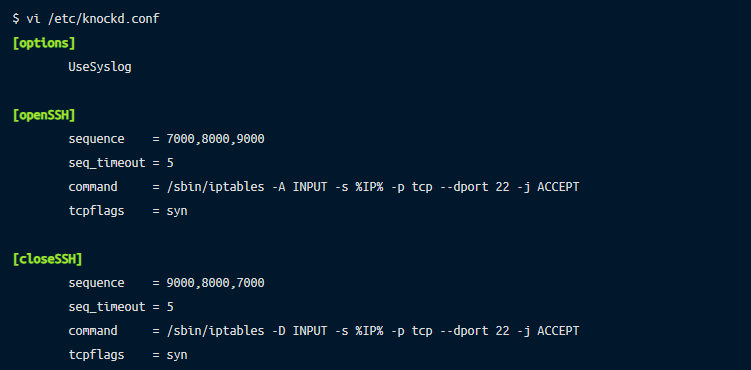
In the config file, let’s first understand the default config values. In the [openSSH] block,
sequence is a collection of port numbers that will be considered as a knock sequence.seq_timeout defines how long the sequence will be valid.command holds the iptables command that adds a rule to allow incoming SSH connection from the specified IP address. This command will be only executed if user initiates a valid knock sequence.tcpflags defines the type of TCP packet to be accepted in knock connection. A TCP packet of SYN type is assigned in this case.The main difference between the [openSSH] block and the [closeSSH] block is that the [closeSSH] block has a closing sequence of port numbers and iptables command that removes the rule that is inserted in the [openSSH] block.
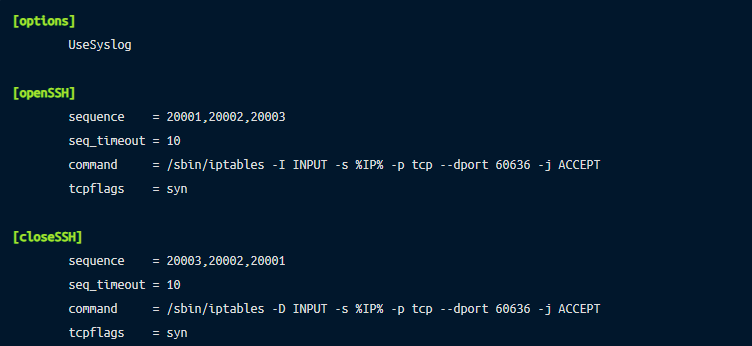
Below is the reference final config file. Notice we’ve changed the open sequence values to 20001, 20002, 20003 as the default ones (7000,8000,9000) are well-known values. Similarly, we have also updated the default closing sequence. We also changed the port 22 to 60636 since we updated the SSH port to this value in the prior step. Also, notice that in the [openSSH] block, we change the iptables command value from -A to -I, indicating that this iptables rule will open the port and will be the first rule to be executed. Lastly, we also increased the timeout value from 5 to 10 because 5 seconds is a small window to initiate SSH connection right after the knock sequence.
Once that’s done, save the changes and exit the file.
We have to specify the name of the network interface in which knockd should listen. Here, we use ip addr command to check the list of network interfaces associated with the server and pick an interface name we want knockd to listen on.
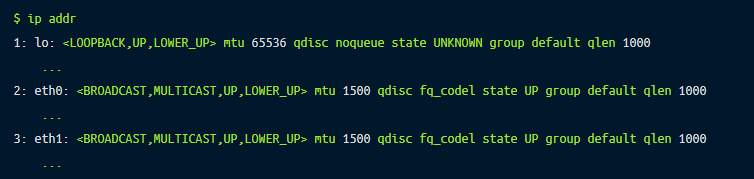
In this case, eth0 is the interface which binds to a public IP address. So I will use this interface to configure knockd.
Next, edit the knockd config file.
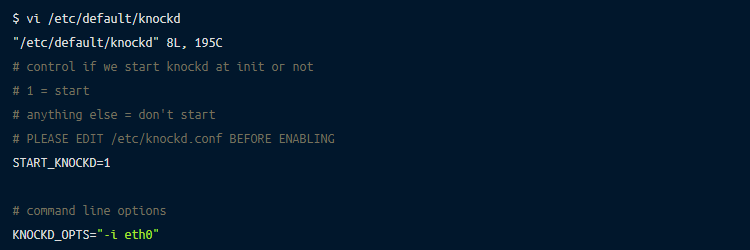
Save the changes and exit the file. Start the knockd service now:
You should also enable the knockd service so that it is started next time when the server is started.
Since we want port 60636 to be open dynamically using knockd, we will block access to this port by default. We will use iptables command to do this.
First, execute the following command so that it does not break our current active connection:
Now, execute iptables command to block all incoming SSH connection on port 60636 by default:
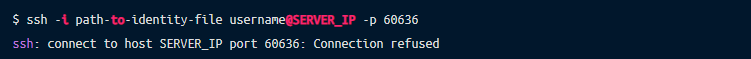
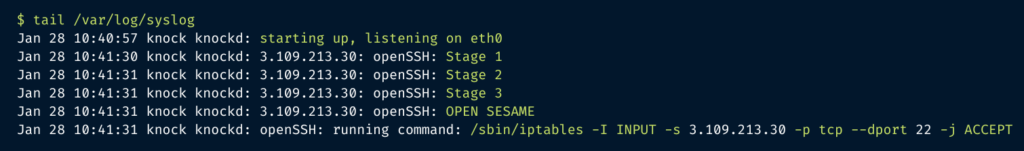
Now try to connect to SSH server again and you should receive a “Connection refused” response:
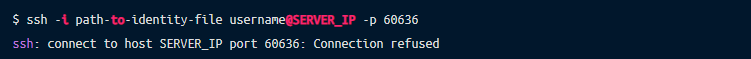
Our Linux server is now configured with knockd, and SSH port will only be opened to a specific IP which can successfully present a knock sequence.
We have changed the default SSH port and implemented knockd to open port 60636 only if the correct knock sequence is provided. Let’s test this now!
Since we have configured knockd to listen on TCP SYN packet on ports 20001, 20002, and 20003 as a knock sequence, we can use any network tool that allows initiating TCP connection to these specific ports. Below, we show how to do it using knockd and telnet.
First, install knockd on your client machine.
Then to perform the knock sequence, we will use the knock command as the following:
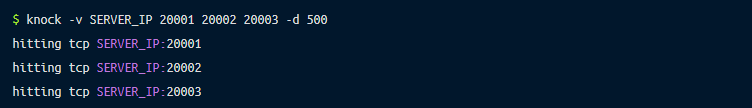
You should now be able to connect the Linux server as you would normally access via SSH:
Once you are done with your SSH access, you can initiate a close sequence as:
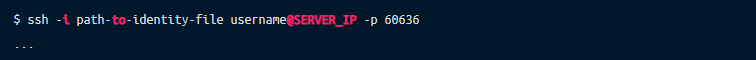
If you are curious about what happens in the server during the knock sequence, you can view the knockd log in syslog, which should look something similar to the following:
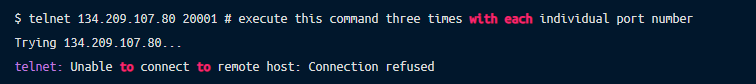
You can also initiate a knock sequence using telnet:
These two methods are the most popular ways to implement security by obscurity. Although this process is fun to implement and see in action, it may not be feasible in production if you have a large number of SSH servers or if you need to automate SSH access. For a similar use case, Remoteler offers a reverse tunneling feature that lets you connect to the server without the risk of exposing the port to the public internet.
Remoteler allows engineers and security professionals to unify access for SSH servers, Kubernetes clusters, web applications, and databases across all environments. Compared to OpenSSH, Remoteler is a secure alternative and offers features such as certificate-based SSH authentication, SSH audit reporting, and SSH role-based access control. Remoteler is open source and super easy to get started. Give it a try.